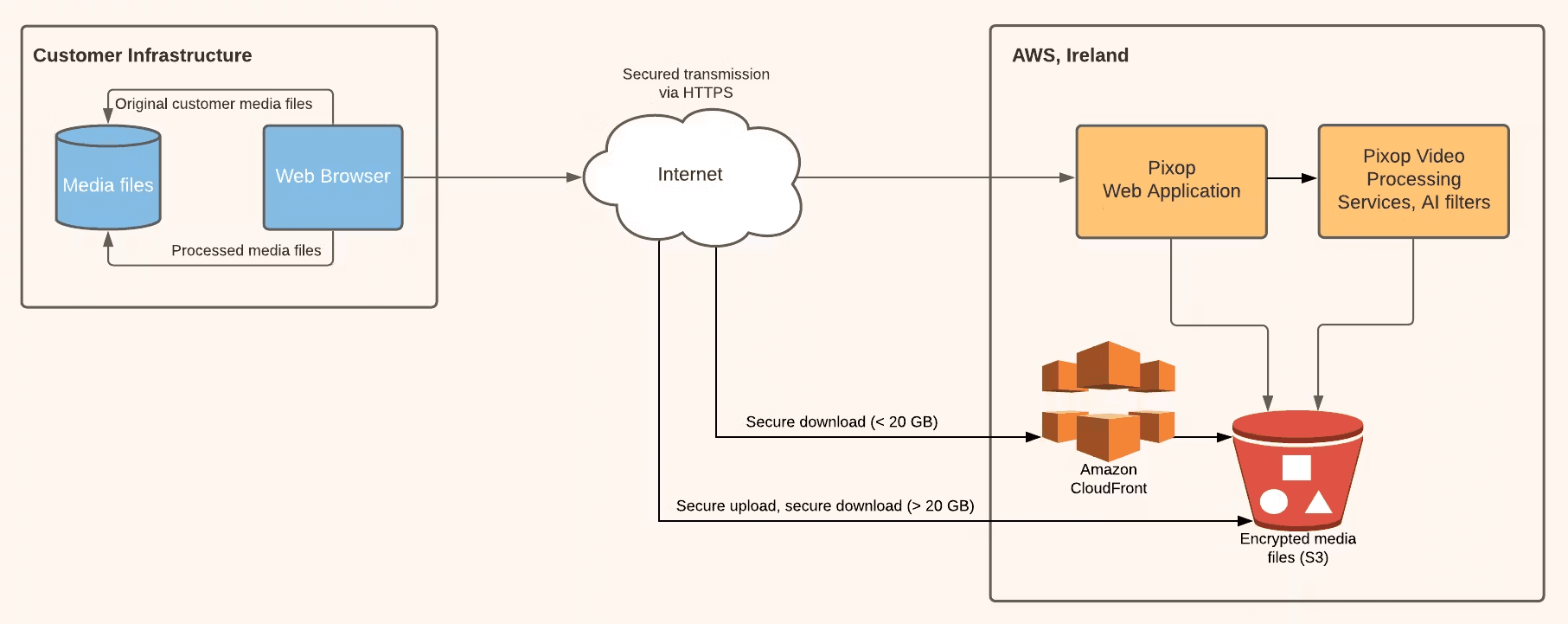
Secure AI-powered video processing: Upload, enhance, and retrieve media seamlessly via Pixop's cloud-based workflow.
Security at Pixop
We take your security very seriously at Pixop. Here's a look at how data is stored, encrypted and transmitted in our systems.
Latest update

Jon Frydensbjerg
Sep 7, 2021
Posted originally
As a SaaS company working in the entertainment and broadcast media industry, we appreciate how serious our responsibility is towards protecting the data and IP of our users. While we won't reveal too much about the specifics of how we keep our platform secure (as doing so may expose it to exactly the kind of vulnerability we work to avoid), here is a general idea of the steps we ensure to protect our users on both our web app and REST API.
Data processing
We ensure that your data is encrypted at every stage of the process — including encryption in transit when it is transmitted inside AWS infrastructure.
Data is not tunneled through our own endpoints. It is uploaded directly to S3 (Encrypted Media Files Bucket) for performance reasons.
Downloads are fronted via either CloudFront (AWS CDN) or received directly from S3 for very large files (>20 GB).
Once a user uploads a file, it goes directly to the Encrypted Media Files Bucket (S3) after some coordination with the web app. This ensures that all your data is completely secure. The web app is also in charge of finalizing the upload. Once the file has been uploaded to the Encrypted Media Files Bucket, you can view it within the app and begin processing.
Once you cue up a processing job by clicking on the video, choosing settings in the process tool and clicking 'process' (or 'create preview', as the case may be), the web app fetches the files from the Encrypted Media Files Bucket and applies your settings to begin processing the video. Once the processing job is done, the processed file is stored and available in the Encrypted Media Files Bucket. It can be viewed in the web app.
When you click on the 'download' button to begin downloading the video, one of two things happens: if the file is below 20GB, the download request is faster and is done via Amazon CloudFront. If the file is above 20GB, it is downloaded directly from the Encrypted Media Files Bucket.
Data Centre Security
Pixop relies completely on cloud infrastructure and our services are based in AWS Ireland.
AWS Ireland have a number of security protocols and measures in place, including encryption of data at rest and in transit using multiple encryption layers, frequent audits of AWS environments and ongoing data centre risk management.
Protection from Data Loss, Corruption
Pixop relies on managed services such as DynamoDB, Heroku and RDS.
All databases are kept separate to prevent corruption and overlap, with multiple layers of logic that segregate user accounts from each other.
Account data is mirrored and regularly backed up off site.
Application Level Security
Pixop account passwords are hashed via bcrypt. Our own staff can't even view them. If you lose your password, it can't be retrieved—it must be reset.
All login pages pass data via TLS.
The entire Pixop application is encrypted with TLS.
Compliant PCI Service Provider Level 1 Certification
Pixop's credit card processing vendor, Stripe, uses security measures to protect your information both during the transaction and after it is complete.
Stripe has been audited by a PCI-certified auditor and is certified to PCI Service Provider Level 1. This is the most stringent level of certification available in the payments industry.
To accomplish this, they use the best-in-class security tools and practices, including HTTPS and HSTS for secure connections, encryption at rest with AES-256 and separate machines to store decryption keys.
None of Stripe’s internal servers and daemons can obtain plaintext card numbers but can request that cards are sent to a service provider on a static allowlist.
Stripe’s infrastructure for storing, decrypting, and transmitting card numbers runs in a separate hosting environment, and doesn’t share any credentials with Stripe’s primary services (API, website, etc.).
GDPR
Pixop is headquartered in the EU and is bound by the European Union's GDPR framework.
Responsible Disclosure
If you’ve discovered a vulnerability in the Pixop application, please don’t share it publicly. Instead, please write to us at help@pixop.com or use the chat function on our website.
If you believe your account has been compromised or you are seeing suspicious activity on your account, please email help@pixop.com or use the chat function on our website.
Our latest posts
Stay in the loop
Sign up